Month: Mar 2026
Azure Alert: Default Outbound Access Ends March 31st
Is your “Internet-less” VM about to lose its connection? Here is the fix.
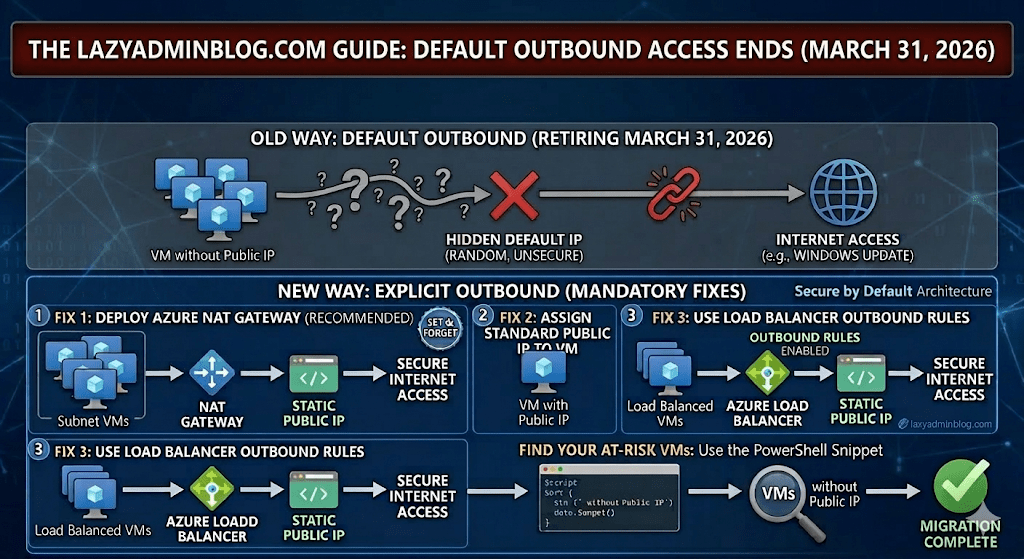
For years, Azure allowed Virtual Machines without an explicit outbound connection (like a Public IP or NAT Gateway) to “cheat” and access the internet using a default, hidden IP. That ends on March 31st 2026. If you haven’t transitioned your architecture, your updates will fail, your scripts will break, and your apps will go dark.
1. What exactly is changing?
Microsoft is moving toward a “Secure by Default” model. The “Default Outbound Access” (which was essentially a random IP assigned by Azure) is being retired. From now on, you must explicitly define how a VM talks to the outside world.
2. The Three “Lazy Admin” Solutions
You have three ways to fix this before the deadline. Choose the one that fits your budget and security needs:
Option A: The NAT Gateway (Recommended)
This is the most scalable way. You associate a NAT Gateway with your Subnet. All VMs in that subnet will share one (or more) static Public IPs for outbound traffic.
- Pro: Extremely reliable and handles thousands of concurrent sessions.
- Con: There is a small hourly cost + data processing fee.
Option B: Assign a Public IP to the VM
The simplest “Quick Fix.” Give the VM its own Standard Public IP.
- Pro: Immediate fix for a single server.
- Con: It’s a security risk (opens a door into the VM) and gets expensive if you have 50 VMs.
Option C: Use a Load Balancer
If you already use an Azure Load Balancer, you can configure Outbound Rules.
- Pro: Professional, enterprise-grade setup.
- Con: More complex to configure if you’ve never done it before.
3. How to find your “At Risk” VMs
Don’t wait for March 31st 2026 to find out what’s broken. Run this PowerShell snippet to find VMs that might be relying on default outbound access:
# Find VMs without a Public IP in a specific Resource Group$VMs = Get-AzVM -ResourceGroupName "YourRGName"foreach ($vm in $VMs) { $nic = Get-AzNetworkInterface -ResourceId $vm.NetworkProfile.NetworkInterfaces[0].Id if ($null -eq $nic.IpConfigurations.PublicIpAddress) { Write-Host "Warning: $($vm.Name) has no Public IP and may rely on Default Outbound Access!" -ForegroundColor Yellow }}🛡️ Lazy Admin Verdict:
If you have more than 3 VMs, deploy a NAT Gateway. It’s the “Set and Forget” solution that ensures you won’t get a 2 AM call on April 1st when your servers can’t reach Windows Update.
LazyAdminBlog.com : M365 E7: The “Super SKU” is Here (And it Costs $99)
Is the new ‘Frontier Suite’ a lazy admin’s dream or a budget nightmare?
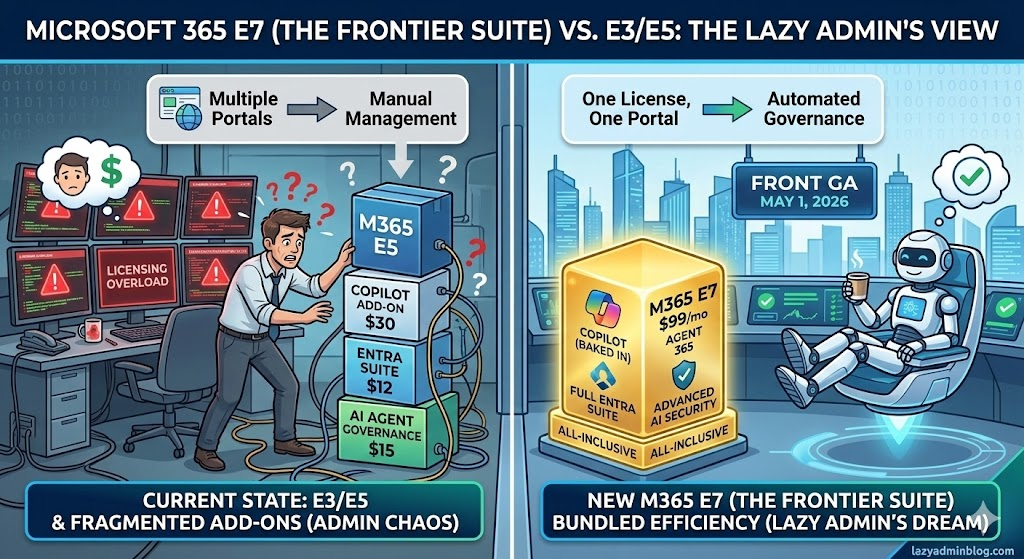
After 11 years of E5 being the king of the mountain, Microsoft has officially announced its successor: Microsoft 365 E7. Launching May 1, 2026, this isn’t just a minor update—it’s a $99/month powerhouse designed for an era where AI agents are treated like actual employees.
1. What’s inside the E7 Box?
If you’ve been “nickel and dimed” by add-on licenses for the last two years, E7 is Microsoft’s way of saying “Fine, here’s everything.”
- Microsoft 365 Copilot (Wave 3): No more $30 add-on. It’s baked in, including the new “Coworker” mode developed with Anthropic.
- Agent 365: This is the big one. A brand-new control plane to manage, secure, and govern AI agents across your tenant.
- Microsoft Entra Suite: You get the full identity stack, including Private Access (ZTNA) and Internet Access (SSE), which were previously separate costs.
- Advanced Security: Enhanced features for Defender, Intune, and Purview specifically tuned for “Agentic AI” (AI that actually performs tasks, not just answers questions).
2. The $99 Math: Is it worth it?
At first glance, $99 per user per month sounds like a typo. But let’s look at the “Lazy Admin” math:
| Component | Standalone Cost (Est.) |
| M365 E5 | $60 (post-July 2026 hike) |
| M365 Copilot | $30 |
| Agent 365 | $15 |
| Entra Suite Add-on | $12 |
| Total Value | $117/month |
By moving to E7, you’re saving about $18 per user and, more importantly, you stop managing four different license renewals. That is the definition of working smarter.
3. The “Agentic” Shift
Why do we need E7? Because in 2026, agents are becoming “Frontier Workers.” Microsoft’s new stance is that AI agents need their own identities. Under E7, your automated agents get their own Entra ID, mailbox, and Teams access so they can attend meetings and file reports just like a human. E7 provides the governance layer to make sure these agents don’t go rogue and start emailing your CEO the company’s secrets.
📊 Microsoft 365 License Comparison: E3 vs. E5 vs. E7
| Feature Category | M365 E3 | M365 E5 | M365 E7 (Frontier) |
| Monthly Cost | ~$36.00 | ~$57.00 | $99.00 |
| Core Productivity | Full Apps + Teams | Full Apps + Teams | Full Apps + Teams |
| Security | Basic (Entra ID P1) | Advanced (Entra ID P2) | Autonomous (P3) |
| Compliance | Core eDiscovery | Inner Risk + Priva | Agentic Governance |
| AI Integration | Add-on Required | Add-on Required | Native Copilot Wave 3 |
| Specialized Tooling | None | Power BI Pro | Agent 365 (Suite) |
| Threat Protection | Defender for Endpoint | Defender XDR Full | Quantum Defender |
| Endpoint Mgmt | Intune (Basic) | Intune (Plan 2) | Autopilot Frontie |
🛡️ Lazy Admin Verdict:
- Upgrade to E7 if: You already have 50%+ Copilot adoption and you’re starting to build custom AI agents in Copilot Studio.
- Stay on E5 if: You’re still fighting with users to turn on MFA and haven’t touched AI yet.
📚 References & Further Reading
- Official Microsoft Announcement: Introducing the First Frontier Suite built on Intelligence + Trust – The primary source for E7 pricing and the “Wave 3” Copilot vision.
- Technical Deep Dive: Secure Agentic AI for your Frontier Transformation – Details on how Agent 365 integrates with Defender and Purview.
- Partner Insights: Leading Frontier Firm Transformation with Microsoft 365 E7 – Great for understanding the licensing shift from an MSP/Partner perspective.
- Analysis: M365 E7 to Launch May 1 for $99 Per User Per Month – Independent analysis of the “Super SKU” value proposition.
LazyAdminBlog.com : Guide to the Entra ID Passkey Rollout (March 2026)
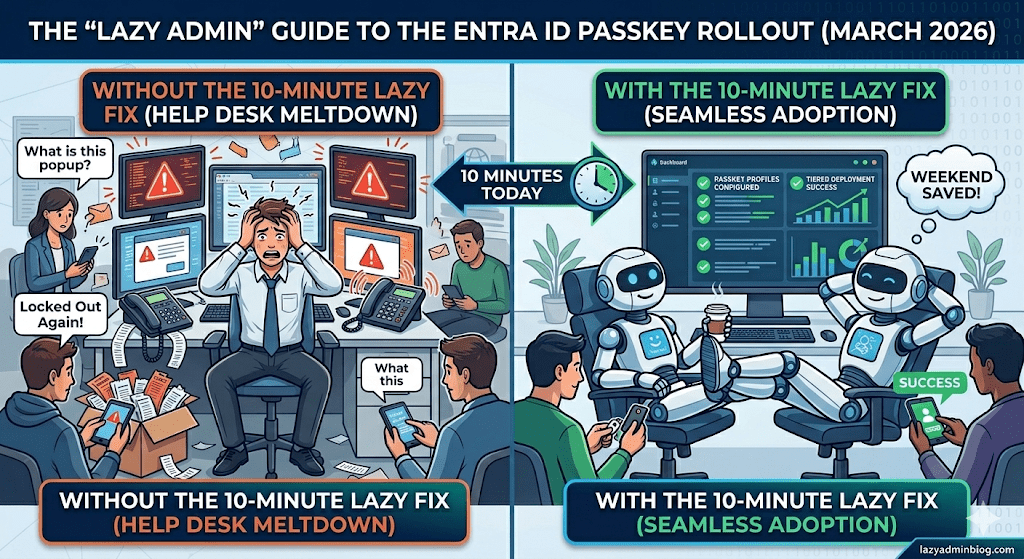
How to avoid 500 helpdesk tickets by spending 10 minutes in the Admin Center today.
If you woke up this morning to find a new “Default Passkey Profile” in your Entra tenant, don’t panic. Microsoft is officially “encouraging” (read: forcing) the world toward phishing-resistant auth. As a Lazy Admin, your goal isn’t to fight the change—it’s to control it so it doesn’t control your weekend.
1. The Big Change: Passkey Profiles
Previously, FIDO2 was a simple “On/Off” switch. Now, we have Passkey Profiles.
- The Default Behavior: If you didn’t opt-in, Microsoft has created a “Default Profile” for you.
- The Trap: If you had “Enforce Attestation” set to No, Microsoft is now allowing Synced Passkeys (iCloud Keychain, Google Password Manager). This means users can put corporate credentials on their personal iPhones.
2. The “Lazy” Strategy: Tiered Security
Don’t treat your CEO and your Summer Intern the same way. Use the new Group-Based Profiles to save yourself the headache of “One Size Fits None.”
| User Group | Recommended Profile | Why? |
| IT Admins | Device-Bound Only | Requires a physical YubiKey or Windows Hello. No syncing to the cloud. |
| Standard Users | Synced & Device-Bound | Maximum convenience. If they lose their phone, iCloud/Google restores the key. Zero helpdesk calls. |
| Contractors | AAGUID Restricted | Only allow specific hardware models you’ve issued to them. |
3. Avoid the “Registration Deadlock”
Many admins are seeing “Helpdesk Hell” because their Conditional Access (CA) policies are too strict.
The Problem: You have a policy requiring “Phishing-Resistant MFA” to access “All Apps.” A user tries to register a passkey, but they can’t log in to the registration page because… they don’t have a passkey yet.
The Lazy Fix: Exclude the “Register security information” user action from your strictest CA policies, or better yet, issue a Temporary Access Pass (TAP) for 24 hours. A TAP satisfies the MFA requirement and lets them onboard themselves without calling you.
🛠️ The 5-Minute “Lazy Admin” Checklist
- [ ] Check your Attestation: Go to Security > Authentication Methods > Passkey (FIDO2). If you want to block personal iPhones, set Enforce Attestation to Yes.
- [ ] Kill the Nudges: If you aren’t ready for the rollout, disable the “Microsoft-managed” registration campaigns before they start bugging your users on Monday.
- [ ] Review AAGUIDs: If you only use YubiKeys, make sure their AAGUIDs are explicitly whitelisted in your Admin profile.
Bottom Line: Spend 10 minutes setting up your profiles today, or spend 10 hours resetting MFA sessions next week. Choose wisely.